Trouble Shooting(3)Networks of a mobile network operator
●After with SYNESIS(1)
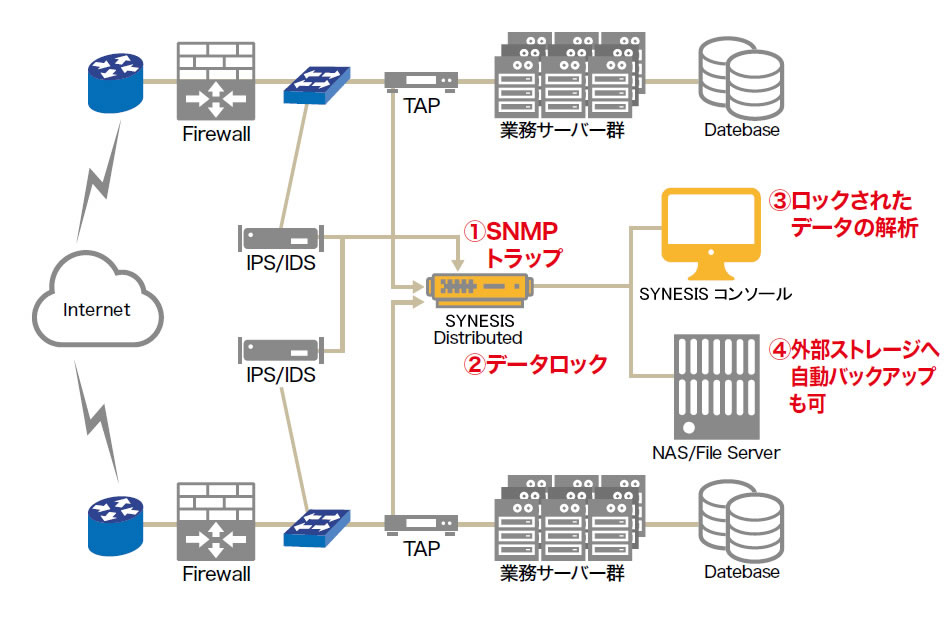
SYNESIS can use SNMP traps from IDS/IPS or other network devices as triggers to lock the packets captured within a few minutes before and after the trigger so that those packets will not be overwritten. Analyzing the locked packets allows for identifying attack packets and leaked data.
●After with SYNESIS(2)
System administrators can set SYNESIS to automatically save captured data onto such external storage as NSA on pre-defined schedules.


